Digital life in the UK is more connected than ever. We shop online, manage banking apps on the go, stream entertainment across devices, and control smart home systems from our phones. While this convenience saves time, it also increases exposure to cyber threats that most people rarely think about until something goes wrong.
Every connected device creates another possible entry point for hackers, scammers, or malicious software. From smartphones and laptops to smart TVs and doorbell cameras, modern households are surrounded by technology collecting and transmits data constantly.
Even something as simple as downloading a mobile game can carry hidden risks. A popular-looking tower rush game app may request unnecessary permissions such as access to contacts, location tracking, or microphone controls. Many users approve these requests without checking what data they are actually sharing.
Understanding how these risks work is one of the most practical ways UK users can improve their digital safety.
Why Cybersecurity Matters More Than Ever in the UK
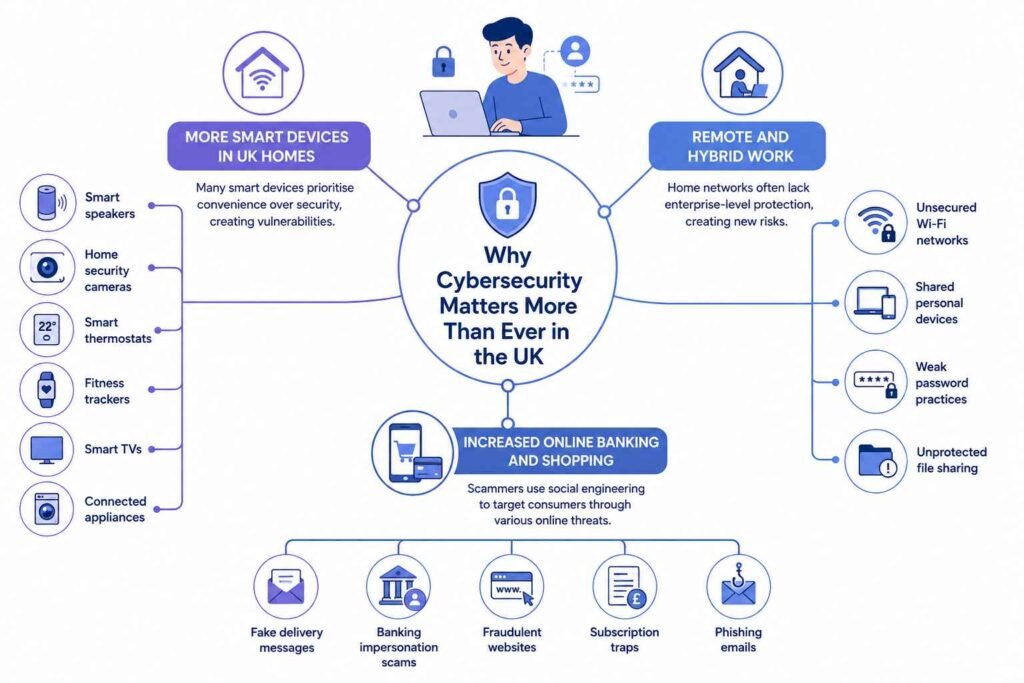
Cybercrime has become one of the fastest-growing forms of crime across the UK. Online scams, phishing attacks, identity theft, and ransomware incidents affect both individuals and businesses every day.
Several factors are contributing to this rise:
More Smart Devices in UK Homes
Modern UK households now commonly use:
- Smart speakers
- Home security cameras
- Smart thermostats
- Fitness trackers
- Smart TVs
- Connected appliances
Many of these devices prioritise convenience over security. Weak passwords, outdated firmware, and poor encryption can create vulnerabilities that hackers exploit.
Remote and Hybrid Work
Since remote working became more common, millions of people now access office systems from home networks that may not have enterprise-level protection.
This creates new risks such as:
- Unsecured Wi-Fi networks
- Shared personal devices
- Weak password practices
- Unprotected file sharing
For UK businesses, hybrid work has made cybersecurity awareness far more important than before.
Increased Online Banking and Shopping
The UK has one of the largest digital commerce markets in Europe. While online payments are convenient, scammers continue targeting consumers through:
- Fake delivery messages
- Banking impersonation scams
- Fraudulent websites
- Subscription traps
- Phishing emails
Many attacks rely on social engineering rather than advanced hacking.
Common Cybersecurity Threats UK Users Face
Understanding the most common online threats makes them easier to avoid.
| Threat Type | How It Works | Common UK Examples |
|---|---|---|
| Phishing Emails | Fake emails steal login details | HMRC scams, fake Royal Mail texts |
| Malware | Malicious software infects devices | Fake downloads or browser popups |
| Ransomware | Files become locked until payment | Business data attacks |
| Identity Theft | Criminals misuse personal details | Banking fraud and fake accounts |
| Public Wi-Fi Risks | Unsecured networks expose data | Cafes, airports, hotels |
| Fake Apps | Apps collect unnecessary permissions | Unverified gaming or utility apps |
How Everyday Apps Collect More Data Than Expected
Many people assume apps only collect the information they need. In reality, some apps request far more access than necessary.
For example, gaming apps, shopping platforms, and free utilities may ask for:
- Contact access
- Camera permissions
- Continuous location tracking
- Storage access
- Microphone controls
The problem is not always the app itself. The issue appears when large amounts of user data are stored centrally. A single data breach can expose:
- Email addresses
- Passwords
- Payment details
- Location history
- Personal photos
- Device information
This is why reviewing app permissions regularly has become an important part of keeping your data protected online.
Practical Cybersecurity Habits for UK Users
Cybersecurity does not require advanced technical knowledge. Small habits make a significant difference over time.
Use Strong and Unique Passwords
One of the biggest mistakes people make is reusing passwords across multiple accounts.
A password manager can help generate and store secure passwords safely.
Good passwords should:
- Be long
- Include multiple character types
- Avoid personal details
- Never be reused
Enable Multi-Factor Authentication
Multi-factor authentication adds an extra layer of protection by requiring:
- A password
- Plus a code from your phone or email
Even if a password is stolen, attackers still cannot access the account easily.
Keep Devices Updated
Software updates often include critical security patches.
This applies to:
- Phones
- Laptops
- Browsers
- Smart TVs
- Routers
- Smart home devices
Ignoring updates leaves devices vulnerable to known exploits.
Be Careful With Public Wi-Fi
Public Wi-Fi networks in cafés, airports, or shopping centres can expose personal data.
When using public Wi-Fi:
- Avoid banking transactions
- Avoid entering passwords
- Use a VPN if possible
- Disable automatic connections
Check App Permissions Regularly
Before installing any app:
- Review permissions carefully
- Avoid unnecessary access requests
- Download only from official stores
- Read reviews carefully
If an app requests more access than it reasonably needs, that is often a warning sign.
Cybersecurity for Families and Young Users
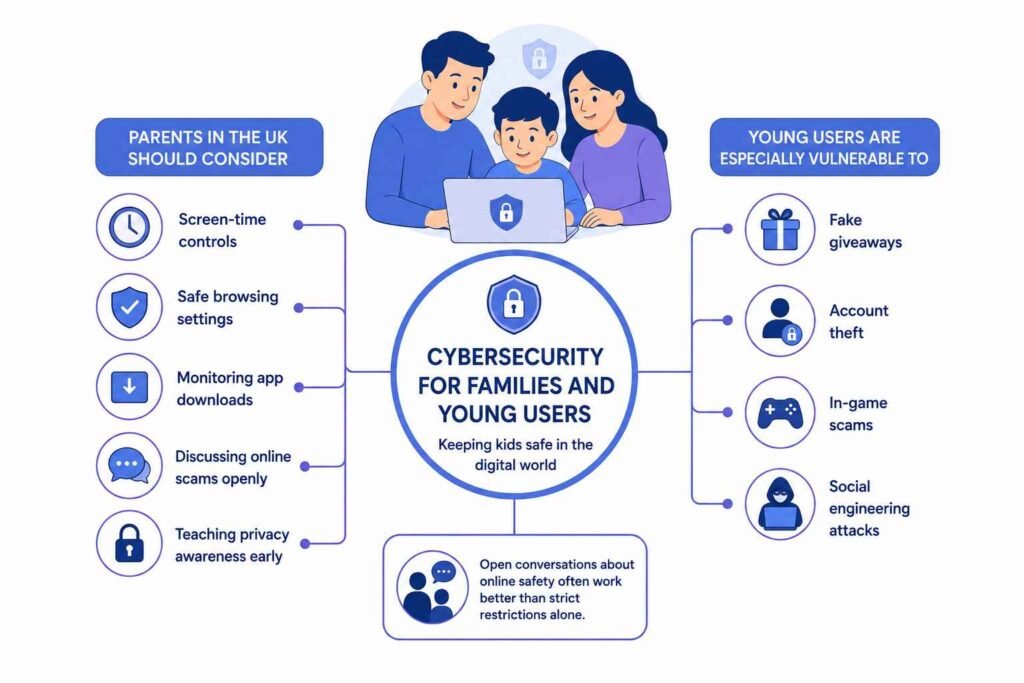
Children and teenagers now spend significant amounts of time online through gaming, streaming, education, and social media.
Parents in the UK should consider:
- Screen-time controls
- Safe browsing settings
- Monitoring app downloads
- Discussing online scams openly
- Teaching privacy awareness early
Young users are especially vulnerable to:
- Fake giveaways
- Account theft
- In-game scams
- Social engineering attacks
Open conversations about online safety often work better than strict restrictions alone.
Role of AI in Modern Cybersecurity
Artificial intelligence is changing cybersecurity rapidly.
How AI Helps Defenders
AI systems can:
- Detect unusual behaviour
- Identify suspicious logins
- Monitor network activity
- Spot fraud patterns quickly
Banks and large UK organisations increasingly rely on AI-driven monitoring systems.
How Attackers Use AI
Unfortunately, cybercriminals also use AI tools to:
- Generate realistic phishing emails
- Create fake customer support chats
- Mimic writing styles
- Automate scam campaigns
This makes online scams harder to recognise than before.
Cybersecurity Tips for UK Small Businesses
Small businesses are increasingly targeted because attackers assume security is weaker.
Basic protection measures include:
| Security Measure | Why It Matters |
|---|---|
| Staff training | Reduces phishing risks |
| Regular backups | Helps recover from ransomware |
| Multi-factor authentication | Prevents account takeovers |
| Access controls | Limits damage from breaches |
| Security monitoring | Detects threats earlier |
| Secure cloud storage | Protects business data |
Looking Ahead: The Future of Digital Security
Technology will continue evolving quickly.
Future cybersecurity challenges may involve:
- AI-generated scams
- Smart city vulnerabilities
- Biometric data protection
- Connected healthcare devices
- Quantum computing threats
At the same time, security systems are becoming smarter, more automated, and more user-friendly.
The long-term goal is not to eliminate all cyber threats. It is reducing risks enough that digital life remains safe, practical, and trustworthy.
Final Thoughts
Cybersecurity is no longer just an issue for IT professionals or large corporations. It affects everyone using smartphones, online banking, social media, smart devices, or connected services.
For UK users, the most effective protection often comes from simple daily habits:
- Using stronger passwords
- Updating devices regularly
- Checking app permissions
- Avoiding suspicious links
- Staying aware of modern scams
Technology will always continue changing. So will cyber threats. The best defence is staying informed, cautious, and proactive while enjoying the convenience digital life offers.
Disclaimer
This article is intended for informational and educational purposes only and should not be considered professional cybersecurity, legal, or financial advice. Online threats and security risks continue to evolve, and readers should consult qualified cybersecurity professionals or official UK government guidance for specific security concerns or business protection strategies.
References
- National Cyber Security Centre (NCSC). Cyber Aware Guidance for Individuals and Businesses. UK Government.
- UK Government Cyber Security Breaches Survey 2025. Department for Science, Innovation and Technology.
- Verizon. 2025 Data Breach Investigations Report.
- IBM Security. Cost of a Data Breach Report 2025.
- ENISA European Union Agency for Cybersecurity. Threat Landscape Report 2025.
- Hadlington, L. (2017). Human factors in cybersecurity examining the link between Internet addiction, impulsivity, attitudes towards cybersecurity, and risky cybersecurity behaviours. Heliyon, 3(7), e00346. DOI: 10.1016/j.heliyon.2017.e00346
- Wash, R. (2010). Folk models of home computer security. Proceedings of the Sixth Symposium on Usable Privacy and Security. DOI: 10.1145/1837110.1837125
- Parsons, K. et al. (2017). The human aspects of information security questionnaire. Computers and Security, 42, pp. 165–176. DOI: 10.1016/j.cose.2013.12.002
- Albladi, S.M. and Weir, G.R.S. (2020). User characteristics that influence judgment of social engineering attacks in social networks. Human-centric Computing and Information Sciences, 10(1). DOI: 10.1186/s13673-020-00220-9
- European Union Agency for Cybersecurity (ENISA). Guidelines on Security of Internet of Things Devices.